Traditional vulnerability management is failing because security teams prioritize based on technical severity (CVSS) rather than exploitability. This guide compares CVSS vs EPSS, demonstrating how the Exploit Prediction Scoring System uses real-time threat data to predict attacks, allowing you to deprioritize 85% of 'critical' alerts and focus on the vulnerabilities that hackers actually use.
The root cause of this failure? An over-reliance on CVSS (Common Vulnerability Scoring System) as the sole metric for prioritization. While CVSS measures the severity of a vulnerability (how bad it would be IF exploited), it tells you absolutely nothing about the probability of it actually being exploited in the wild.
Enter EPSS (Exploit Prediction Scoring System). This data-driven framework changes the game by answering the question CVSS ignores: "How likely is this to happen to us?"
What is EPSS and How Does It Predict Attacks?
The Exploit Prediction Scoring System (EPSS) is an open, data-driven effort for estimating the likelihood (probability) that a software vulnerability will be exploited in the wild.
Unlike CVSS, which looks at the intrinsic properties of a vulnerability (e.g., "Is it network accessible?"), EPSS looks at threat data. It ingests data from multiple sources to compute a daily probability score for every published CVE.
The 5-Step Prediction Model
EPSS works by continuously learning from real-world data. According to FIRST.org, the model follows this daily cycle:
- Data Collection: It gathers vulnerability metadata (CPE, age, references) and evidence of exploitation from sensors, honeypots, active threat intelligence, and scanning activity.
- Training: The model analyzes the relationship between vulnerability characteristics and observed exploitation.
- Prediction: It acts as a weather forecast for cybersecurity, producing a probability score (0% to 100%) for the next 30 days.
Why is CVSS Failing Modern Security Teams?
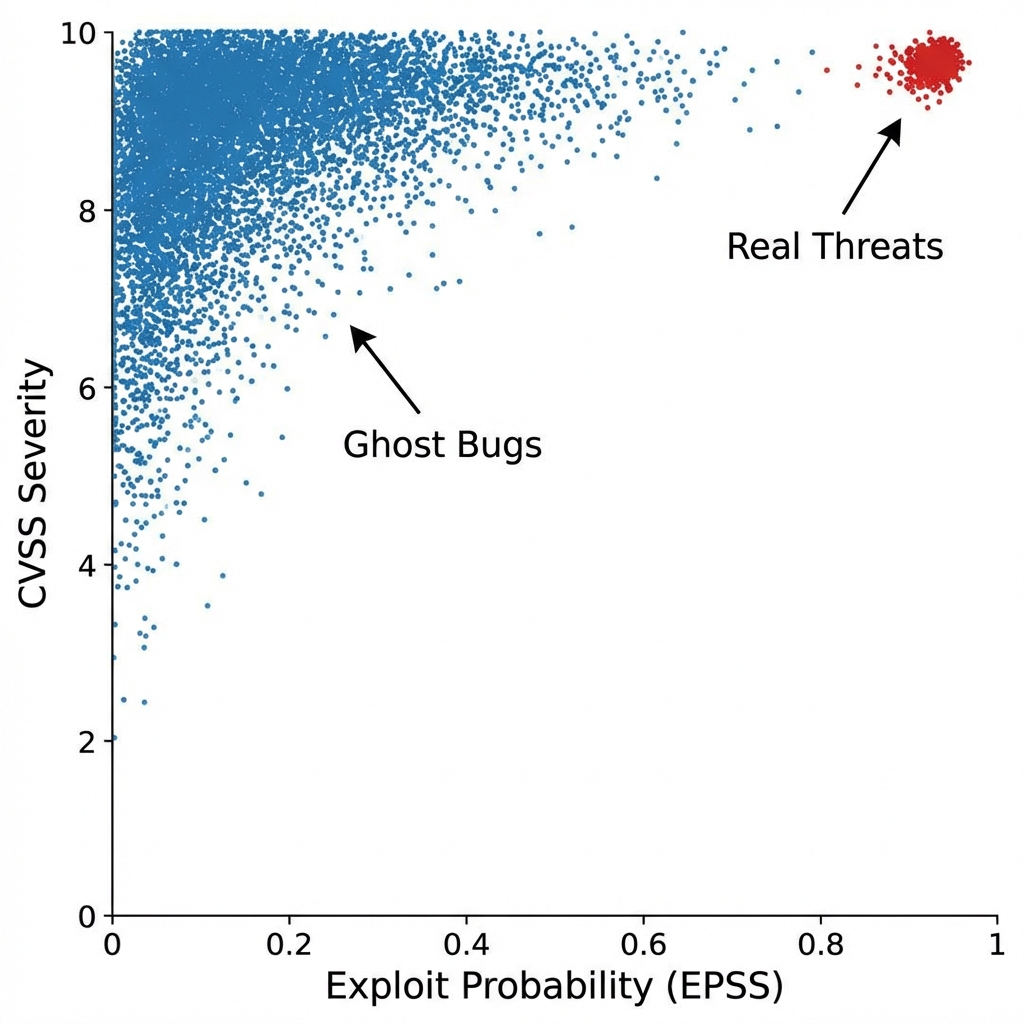
Security engineers face dashboards displaying thousands of vulnerabilities. Legacy tools typically sort by CVSS, resulting in approximately 20% of findings being labeled "Critical" (9.0+). Remediating this volume is simply not feasible because you are fighting against the mathematical reality of remediation.
The data gap
- Fact: Approximately 2% to 7% of published CVEs are exploited in the wild.
- Problem: CVSS rates nearly 57% of vulnerabilities as High or Critical.
- Result: Resources are allocated to "ghost bugs" regarding theoretical flaws that attackers do not utilize.
Perspective: A CVSS 10.0 vulnerability with no known exploit activity presents less immediate risk than a CVSS 7.4 vulnerability currently used in a ransomware campaign.
How to Implement EPSS: A Step-by-Step Guide
Integrating EPSS into your existing workflow does not require buying new tools. You can start today using the free API and CSV data provided by FIRST.org.
Step 1: Ingest the Data
You can download the full CSV daily or query the API for specific CVEs.
# Example: Get score for Log4Shell
curl https://api.first.org/data/v1/epss?cve=CVE-2021-44228Step 2: Define Your Thresholds
Mature organizations typically use a Dual-Threshold strategy:
- Contextual Fix: Patch if EPSS > 10% (Catches ~89% of threats).
- Emergency Fix: Patch if EPSS > 50% (Catches the hottest threats immediately).
Does CVSS v4.0 Solve the Problem?
CVSS v4.0, released in late 2023, introduces the "Threat Metrics" group, which attempts to address the exploitability gap. However, it relies on human analysts to manually set fields like "Exploit Maturity."
The Verdict? CVSS v4.0 is an improvement, but it is still a measure of severity. EPSS remains the only standard for probability. The best practice in 2026 is to use them together: CVSS determines what to fix (impact), and EPSS determines when to fix it (likelihood).
Comparison: CVSS vs. EPSS vs. CISA KEV
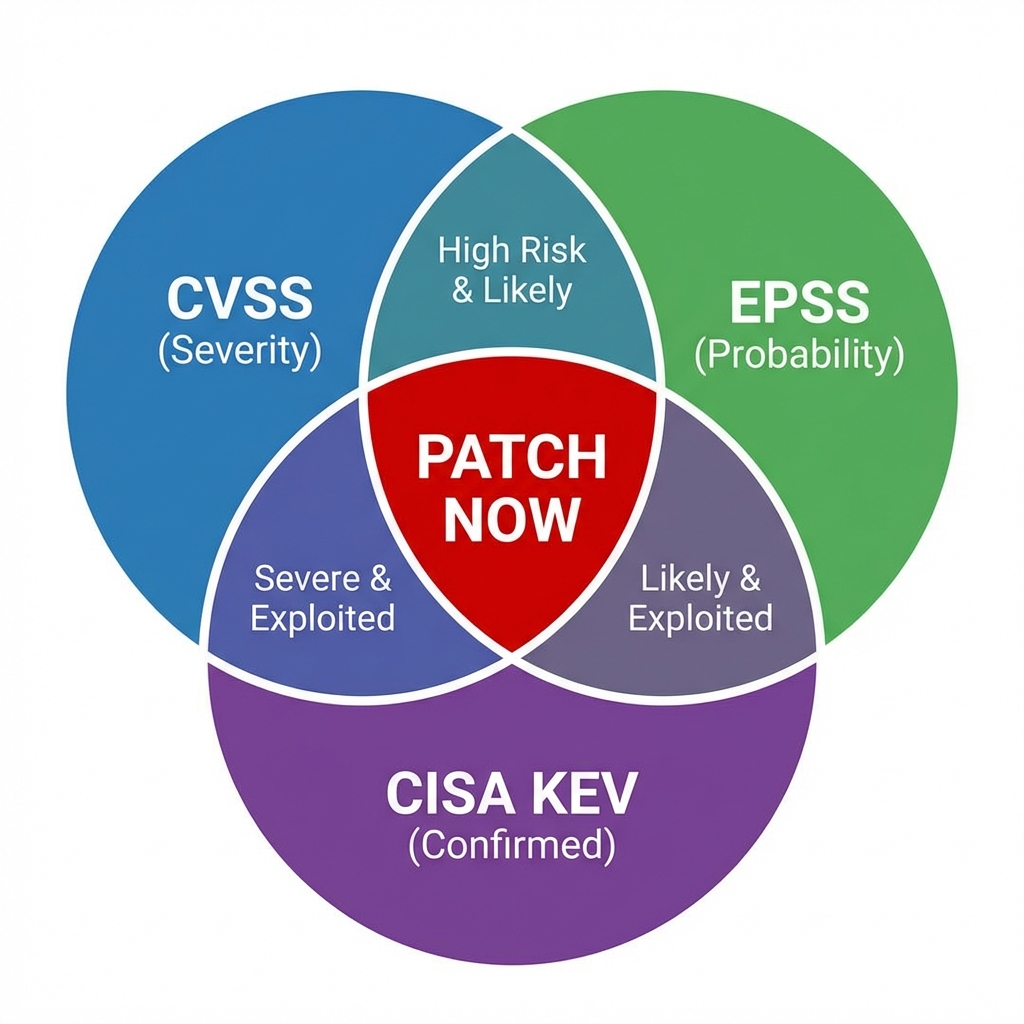
| Feature | CVSS (Severity) | EPSS (Probability) | CISA KEV (Reality) |
|---|---|---|---|
| Question Answered | "How bad *could* the damage be?" | "How *likely* is an attack?" | "Is it happening *right now*?" |
| Primary Metric | Technical complexity, Impact | Threat intel, Exploit code availability | Confirmed attacks |
| Best Use Case | Assessing Audit/Compliance Risk | Daily Prioritization & Triage | Emergency Response |
| False Positive Rate | High (~40-50% noise) | Low (Focuses on <5% of CVEs) | Zero (It is binary) |
Risk-based vulnerability management (RBVM)
Modern Risk-Based Vulnerability Management (RBVM) frameworks utilize a Vulnerability Prioritization Matrix to filter alerts:
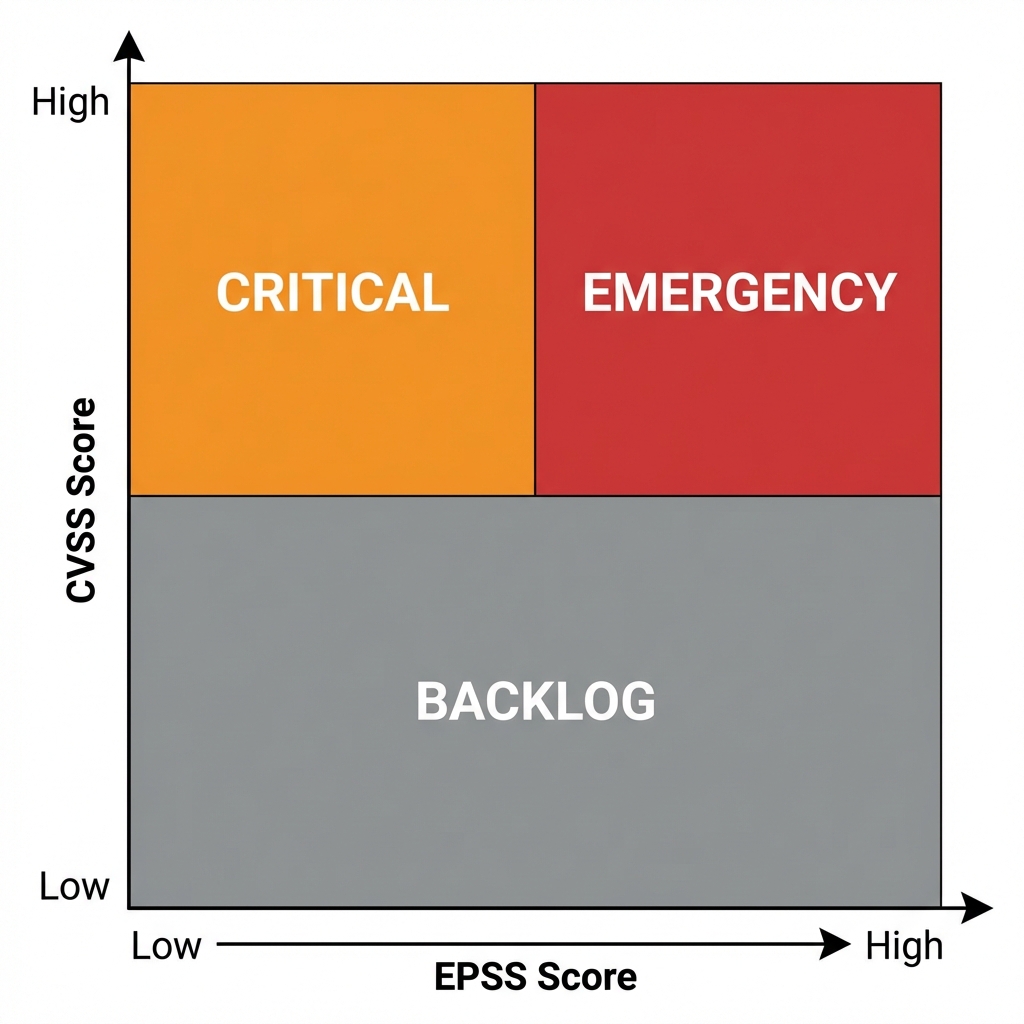
- Tier 1 (Emergency): Listed on CISA KEV or EPSS > 50%. Patch within 24-48 hours.
- Tier 2 (Critical): CVSS > 9.0 and EPSS > 10%. Patch in next standard cycle (7-14 days).
- Tier 3 (Backlog): High CVSS but Low EPSS (<1%). Monitor.
Efficiency gains
By switching from "patch all critical" to a risk-based model, organizations can reduce immediate patch load by approximately 85% while improving coverage of active threats.
Interactive: Check Your "Criticals"
Case Study: CVE-2023-0052
- VulnerabilitySAUTER Controls
- CVSS Score9.8 (CRITICAL)
- EPSS Score0.08% (Low)
- RecommendationDeprioritize. Monitor for changes.
Case Study: CVE-2024-27198
- VulnerabilityTeamCity Auth Bypass
- CVSS Score9.8 (CRITICAL)
- EPSS Score94.5% (High)
- RecommendationPATCH IMMEDIATELY.
Why This Matters for Your Business
Adopting an EPSS-first approach isn't just about better security; it's about efficiency.
When you stop chasing every CVSS 7+, you free up your limited security resources to focus on the 5% of threats that actually pose a risk to your business. This leads to:
- Less Burnout: Your team isn't in constant "firefighting" mode.
- Better Uptime: Fewer panic patches means fewer service disruptions.
- Audit Confidence: You can mathematically justify why you deprioritized a "Critical" bug in favor of a "High" one tailored to your threat model.
The 4 Phases of EPSS Adoption
You don't need to jump straight to automated blocking. Most organizations follow this maturity curve:
Phase 1: Observation
Ingest EPSS scores into your dashboard. Just look at them during triage. Don't change policies yet.
Phase 2: Deprioritization
Use EPSS to downrank "Critical" bugs that have <0.01% probability. Clear the noise first.
Phase 3: Prioritization
Create an "Emergency Lane" for any bug with EPSS > 50%, regardless of its CVSS score.
Phase 4: Automation
Auto-create tickets for EPSS > 20% and auto-close tickets for EPSS < 0.01% (after 90 days).
Frequently Asked Questions
- Does EPSS replace CVSS?
- No. EPSS measures threat (likelihood), while CVSS measures severity (impact). You need both to calculate true risk. A high-severity vulnerability with zero likelihood of exploitation may not need immediate attention.
- How often is the EPSS score updated?
- EPSS scores are updated daily. The model ingests new threat data every 24 hours to provide a dynamic, real-time view of risk. If a widespread exploit kit is released for a vulnerability, you will typically see its EPSS score jump significantly within 24-48 hours.
- Is the EPSS API free to use?
- Yes. FIRST.org provides the EPSS data and API for free to the public to improve global security posture. You do not need an API key for basic query volumes.
- What about 0-day attacks?
- This is one of the distinct limitations of EPSS. Because it relies on observed data and training, it cannot predict a brand new 0-day attack before it happens. For 0-days, you should rely on CISA KEV (Known Exploited Vulnerabilities) list, which is binary (Yes/No) and often updated faster for breaking events.
Ready to see your real risk?
Project Precursor automates this matrix for you. We continuously monitor your stack against CVSS, EPSS, and CISA KEV (Known Exploited Vulnerabilities) lists to filter out the noise and highlight the signal.
Start your free scan today and stop chasing ghosts.